Welcome to the BX Finance User Journey demonstration, where we'll explore 5 use cases Demonstrating how the Ping Identity platform can deliver personalized, Seamless, and secure experiences for your online banking customers.
We'll start at the beginning of the user journey at online customer registration.
Jane is an existing customer of a fictional bank called BX Finance, but has never used their online banking platform.
First, we'll see Jane click the link to register for an online account.
BX Finance uses Ping to collect only the information needed to open an account, With additional information collected later through progressive profiling.
With Ping, all customer data collected is available through REST APIs to use for Personalization and can also be encrypted end to end.
BX Finance also allows customers like Jane to decide how they want to log in at the time of Registration.
Fed up with forgetting passwords?
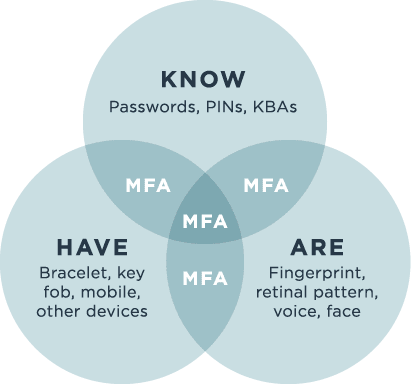
Jane decides to use her MobileIron device or a one-time passcode.
A choice she can make during login.
To use her MobileIron device to log in, all Jane needs to do is download the BX Finance mobile Application with Ping Technology embedded.
Log in with her username and password for the first and last time.
And trust the device.
Jane is now registered.
And our experience continues to be seamless as she's automatically logged in following Registration.
Next, we'll demonstrate passwordless login and Single sign-on.
Jane clicks to sign in after entering her Username, Jane continues with her ideal login experience using Face ID while taking comfort In knowing that email and SMS one-time passcodes are always there, Just in case.
She submits, taps the customizable Push Notification on her phone, authenticates.
And she's in.
Now that she's signed in, Jane is able to Securely access any BX Finance application integrated with the Ping platform.
As an example, BX Finance provides a chatbot for customer service.
Integrated with Ping, Jane's very first digital interaction can be personalized by provisioning Jane's profile attributes, such as length of time as a customer to the service.
Jane closes the chatbot and continues to explore the website.
Next, we'll demonstrate transaction approval.
Jane navigates toward her next B2B finance experience, online money transfer.
Here, Jane enters the accounts, the amounts, and starts the transfer.
Then she completes it by clicking on the push notification and approving the transfer on a Fully customizable approval screen where the customers can view transaction details before Clicking approve.
Next, we'll demonstrate simple consent.
Management.
Jane navigates to Profile and Settings to view Her marketing communications preferences.
With the click of a button, Jane's preferences for SMS and email can be captured and stored Alongside her profile information, where consents can be enforced before communications Are sent and changed by Jane at any point in time.
Of course, enabling customers to self-manage preferences goes hand in hand with ensuring Those preferences are honored.
Let's flip over to view this scenario from the perspective of an email administrator at BX Finance using a popular email marketing tool.
After performing a quick search, you can see again that Jane's email and phone number are Visible, but her physical address is not.
With Ping, no matter what the request contains, only attributes with associated customer Consent will ever be accessible.
Finally, we'll demonstrate advanced consent management and Partner Identity Management.
Beyond honoring communications preferences, you can offer customers partner-based services while allowing them to choose both the partners they share data with and to what extent.
Here, we see common services like Mint and Zelle, but Jane decides to explore Services From any wealth advisor, a wealth management partner of BX Finance.
After reviewing their services, Jane decides to grant any wealth advisor access to view accounts Data, but only for her savings accounts.
From here, using Ping's federated single sign-on capabilities, Jane can navigate directly to any Wealth Advisor Portal without logging in.
Note that only the details of the account she chose to share are displayed, but also that the page is personalized with relevant profile data provisioned to the third-party service, such as her name in the welcome message and ZIP code for geographically Relevant investment seminars.
Finally, to see how consent is enforced with partners, let's flip over to view this scenario From the perspective of Amy Davis, an employee at any Wealth Advisor assigned to Jane's account.
In this case, any wealth advisor is leveraging The Ping platform for employee single sign-on into custom-built portals at some of the Biggest banks in the world, many of which are Ping's customers.
BX Finance is among these, and Amy clicks to log in.
BX Finance ensures that only certain individuals can access this wealth advisor Portal using Ping's authorization capabilities.
Here, we can see Amy look up Jane by her email address and again see that Amy's view is Limited to the savings accounts shared by Jane earlier.
This concludes our demonstration of how the Ping Identity platform can deliver personalized, Seamless, and secure experiences for your online banking customers.
To learn more, talk to your Account Representative or sign up for a free trial Today.